THM | AoC 2025 | Day 09 + SideQuest 2 Key

Day-09: Passwords | Side Quest 2 Key Challenge
SUMMARY
In the first part we crack two encrypted files using dictionary attacks with the "rockyou.txt" wordlist: an encrypted PDF using john directly, and an encrypted ZIP but only after the necessary hash is generated.
For the bonus challenge, we discover an encrypted KeePass Password database (".Passwords.kdbx"), crack its password by first generating the necessary hash with keepass2john and then with john. Inside the database we find a hidden image file ("sq2.png") which contains the Side Quest 2 key.

Passwords - A Cracking Christmas
- TL;DR: Learn how to crack password-based encrypted files.
- Original Room: TryHackMe | Advent of Cyber 2025 | DAY 09 - Passwords - A Cracking Christmas
STORYLINE
"Sir Carrotbane discovers encrypted files ("North Pole Asset List") on The Best Festival Company's servers that may contain Santa's master gift registry. If cracked, Malhare could control the festive balance between worlds. The conflict hinges on whether the Elves can stop the encryption from being breached before their secrets are exposed"
TAKEAWAY
Password strength is the primary determinant of encryption security. Weak passwords can be guessed; strong, random ones are far harder to crack.
Security also depends on the algorithm and key derivation method—different formats (PDF, ZIP) use different approaches, affecting vulnerability. Legacy encryption methods remain weak, particularly older ZIP encryption, making these files easier to crack than modern schemes.
Encryption protects confidentiality only and cannot prevent offline password guessing once an attacker has the encrypted file. Ultimately, security hinges on password complexity rather than the encryption technology itself.
Attacks Agains Encrypted Files
THEORY
Attackers recover weak passwords by guessing them rather than breaking encryption. The two primary methods are:
- Dictionary attacks | Testing passwords from predefined wordlists containing leaked credentials, common substitutions (like "password123"), and predictable patterns. This approach is fast and effective because many users choose weak passwords.
- Mask attacks | A refined version of brute-force attacks that systematically tries character combinations within a specific format (e.g., three lowercase letters followed by two digits). This narrows the search space, making the attack faster than trying all possible combinations while remaining more thorough than dictionary attacks alone.
Both techniques exploit human password habits rather than defeating cryptography itself.
ATTACK TIPPS
- Simple Dictionary attack with wordlists: "rockyou.txt"; "common-passwords.txt"
- Targeted wordlists: compile company names, project names, data from the internet
- Mask or incremental attacks on short passwords (e.g.
?l?l?l?d?d=3xlowercase-letter+2xdigit) - Use GPU-accelerated creacking
- Beware of your OPSEC: your intensive resource use can be detected and monitored
TOOLS
- PDF: pdfcrack, john (via pdf2john)
- ZIP: fcrackzip, john (via zip2john)
DEFEND TIPPS
- Beware and monitor the following password cracking activity signals:
- process creation, command patterns, potfiles, gpu-artifacts, network-activity, file access
- Cracking binaries: john, hashcat, fcrackzip, pdfcrack, zip2john, pdf2john.pl, 7z, qpdf, unzip, 7za, perl invoking pdf2john.pl
- Command patterns:
--wordlist,-w,--rules,--mask,-a 3,-mand references to "rockyou.txt" or "SecLists" - Potfiles: "~/.john/john.pot", ".hashcat/hashcat.potfile", "jonh.rec"
- Process Creation Capture:
- Windows: Sysmon Event ID 1
(ProcessName="C:\Program Files\john\john.exe" OR
ProcessName="C:\Tools\hashcat\hashcat.exe" OR
CommandLine="*pdf2john.pl*" OR
CommandLine="*zip2john*") - Linux: auditd, execve
auditctl -w /usr/share/wordlists/rockyou.txt -p r -k wordlists_read
auditctl -a always,exit -F arch=b64 -S execve -F exe=/usr/bin/john -k crack_exec
auditctl -a always,exit -F arch=b64 -S execve -F exe=/usr/bin/hashcat -k crack_exec
- Windows: Sysmon Event ID 1
- GPU Artifacts: High sustained GPU utilization, long-running hashcat/john processes in nvidia-smi, and loaded GPU libraries ("nvcuda.dll", "OpenCL.dll", "libcuda.so", "amdocl64.dll").
- Network Activity: Downloads of wordlist files, Git clones of wordlist repos, package installs (
apt install john), GPU driver fetches. - File Access: Unusual repeated reads of encrypted or wordlist files.
RESPONSE PLAYBOOK
- Isolate | Remove the affected computer from the network.
- Collect evidence | Gather system files - triage artifacts like process list, process memory dumps open files - and encrypted files for investigation. Also, backup working directory, wordlists, hash files and shell history.
- Investigate | Check what was accessed, if data was stolen, and whether the activity was authorized.
- Respond | If unauthorized, alert the incident response team, change passwords, and enable multi-factor authentication.
- Improve | Train staff and ensure tools are properly secured to prevent future incidents.
Q & A
Question-1: What is the flag inside the encrypted PDF?
[REDACTED-FLAG]
Let us first confirm the the file types and then decide on the appropriate cracking software to use.
ubuntu@tryhackme:~$ cd Desktop/
ubuntu@tryhackme:~/Desktop$ ls -hla
total 64K
drwxr-xr-x 3 ubuntu ubuntu 4.0K [REDACTED-TIME] .
drwxr-xr-x 21 ubuntu ubuntu 4.0K [REDACTED-TIME] ..
-rw-r--r-- 1 ubuntu ubuntu 42K [REDACTED-TIME] flag.pdf
-rw-r--r-- 1 ubuntu ubuntu 245 [REDACTED-TIME] 11:46 flag.zip
drwxrwxr-x 10 ubuntu ubuntu 4.0K [REDACTED-TIME] 15:25 john
-rwxrwxr-x 1 ubuntu ubuntu 166 [REDACTED-TIME] mate-terminal.desktop
ubuntu@tryhackme:~/Desktop$ file flag*
flag.pdf: PDF document, version 1.7, 1 page(s)
flag.zip: Zip archive data, at least v2.0 to extract, compression method=AES Encrypted
ubuntu@tryhackme:~/Desktop$
We have two target files here: "flag.pdf" and "flag.zip".
First we start with the encrypted PDF file. If we try to open and view the file with atril flag.pdf, we are prompted for a password.
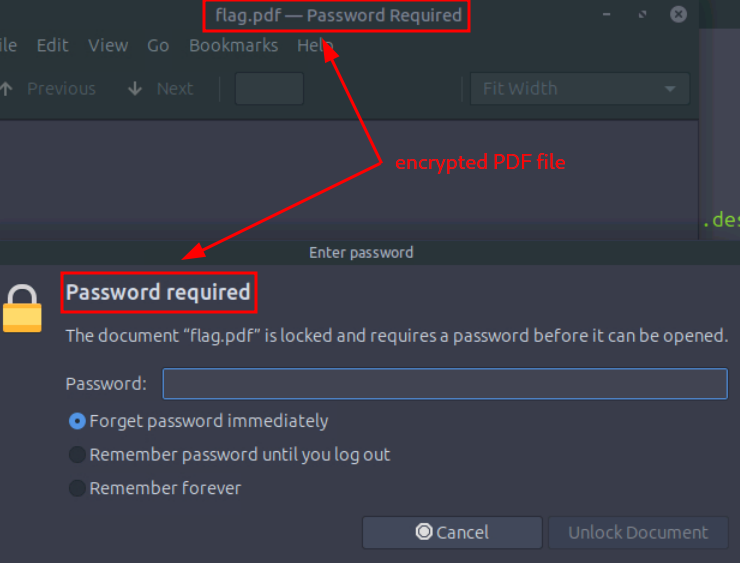
Figure 1: Encrypted PDF File
Given that it's trully encrypted, let's try to crack it using a Dictionary Attack with a basic "rockyou.txt" wordlist.
# -f: filename; -w: wordlist
ubuntu@tryhackme:~/Desktop$ pdfcrack -f flag.pdf -w /usr/share/wordlists/rockyou.txt
PDF version 1.7
Security Handler: Standard
V: 2
R: 3
P: -1060
Length: 128
Encrypted Metadata: True
FileID: 3792b9a3671ef54bbfef57c6fe61ce5d
U: c46529c06b0ee2bab7338e9448d37c3200000000000000000000000000000000
O: 95d0ad7c11b1e7b3804b18a082dda96b4670584d0044ded849950243a8a367ff
found user-password: '[REDACTED-PASSWORD]'
ubuntu@tryhackme:~/Desktop$
Let's use the found password and check on the PDF file with atril flag.pdf. Great, we just found the FLAG for the first question.
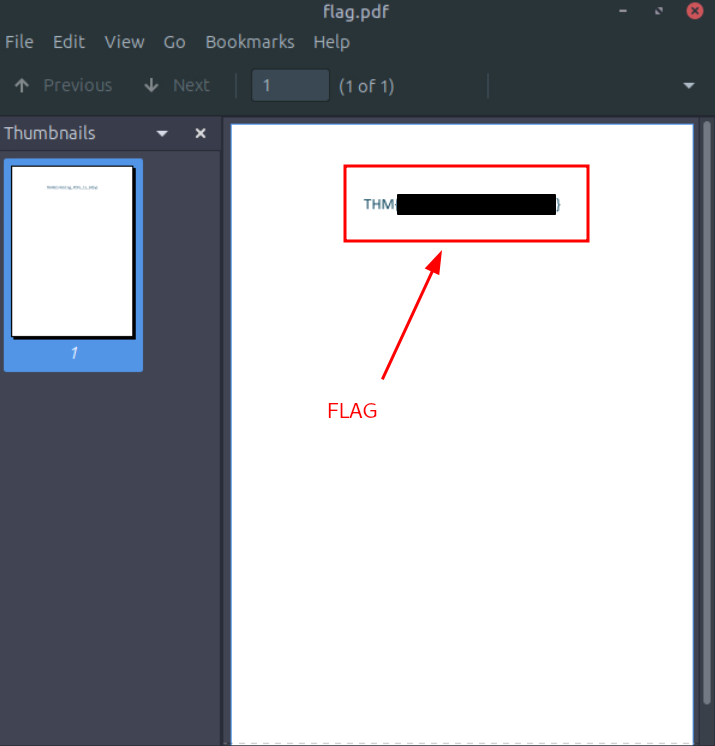
Figure 2: Flag hidden in the decrypted PDF file
Question-2: What is the flag inside the encrypted zip file?
[REDACTED-FLAG]
Before doing anything, let's verify and check on our target archive.
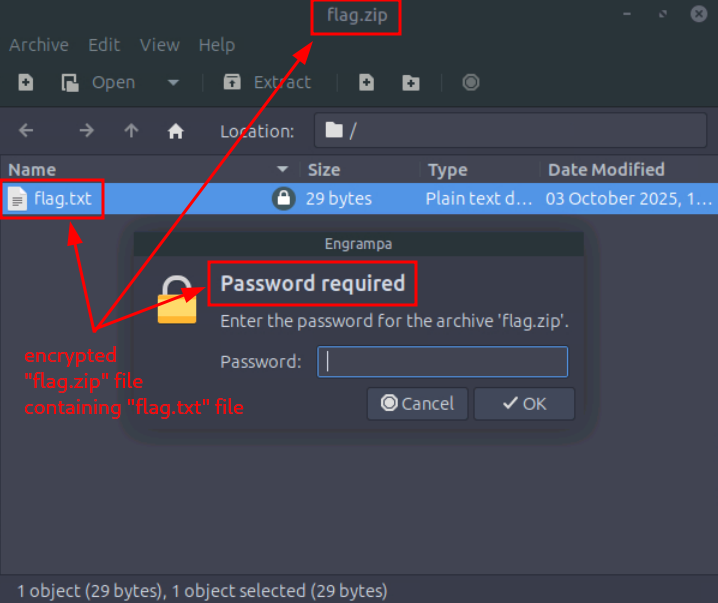
Figure 3: Encrypted Zip Archive
It contains a "flag.txt" file and the archive is trully encrypted and prompts us for a password.
Moving on, for the archive ("flag.zip"), let's first create a hash file with zip2john ("ziphash.txt") that we can use john on to crack it.
ubuntu@tryhackme:~/Desktop$ zip2john flag.zip > ziphash.txt
Let's use the same attack type (Dictionary Attack) with the same wordlist ("rockyou.txt") on the hash.
ubuntu@tryhackme:~/Desktop$ john --wordlist=/usr/share/wordlists/rockyou.txt ziphash.txt
Using default input encoding: UTF-8
Loaded 1 password hash (ZIP, WinZip [PBKDF2-SHA1 256/256 AVX2 8x])
Cost 1 (HMAC size [KiB]) is 1 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, 'h' for help, almost any other key for status
[REDACTED-PASSWORD] (flag.zip/flag.txt)
1g 0:00:00:00 DONE ([REDACTED-TIME]) 1.818g/s 7447p/s 7447c/s 7447C/s [REDACTED-PASSWORD]
Use the "--show" option to display all of the cracked passwords reliably
Session completed
ubuntu@tryhackme:~/Desktop$
Great, it cracked it pretty fast, let's check the results.
ubuntu@tryhackme:~/Desktop$ john ziphash.txt --show
flag.zip/flag.txt:[REDACTED-PASSWORD]:flag.txt:flag.zip:flag.zip
1 password hash cracked, 0 left
ubuntu@tryhackme:~/Desktop$
All that's left is to open the encrypted archive ("file.zip"), decrypt it with the cracked password and check on the FLAG.
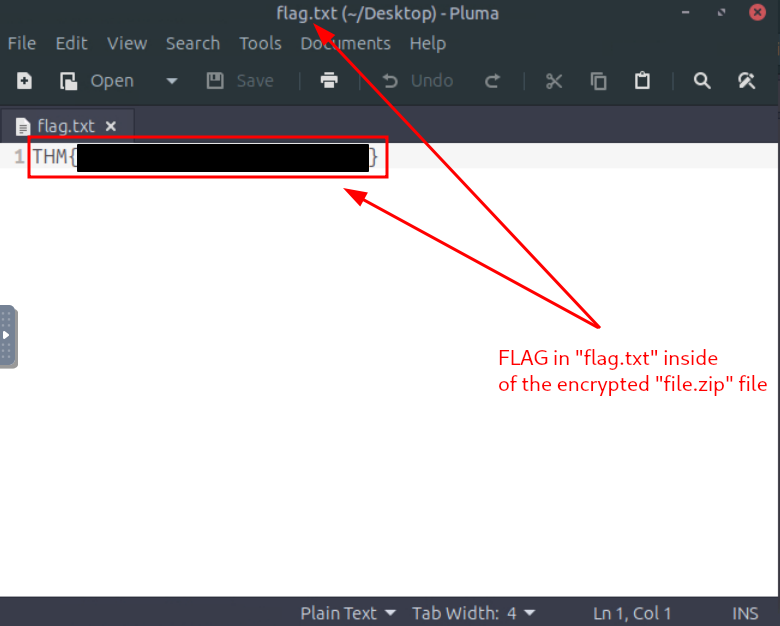
Figure 4: Flag hidden in encrypted Archive
SideQuest-2 Key Challenge
Bonus-Question-1: For those who want another challenge, have a look around the VM to get access to the key for Side Quest 2! Accessible through our Side Quest Hub!
No answer needed
Let's take a quick look at our current environment and see if something stands out.
ubuntu@tryhackme:~$ ls -hla
total 536K
drwxr-xr-x 21 ubuntu ubuntu 4.0K [REDACTED-TIME] .
drwxr-xr-x 3 root root 4.0K [REDACTED-TIME] ..
-rw------- 1 ubuntu ubuntu 410K [REDACTED-TIME] .Passwords.kdbx
[...SNIP...]
ubuntu@tryhackme:~$
Great, we found a potential candidate, a KeePass Password Database named ".Passwords.kdbx". Let's get more details on it:
ubuntu@tryhackme:~$ file .Passwords.kdbx
.Passwords.kdbx: Keepass password database 2.x KDBX
ubuntu@tryhackme:~$
Next, for cracking it, just like we did with the archive file, we need to first create a hash file ("database.hash") from it with the keepass2john module from john-the-ripper.
ubuntu@tryhackme:~$ /snap/john-the-ripper/694/bin/keepass2john .Passwords.kdbx > database.hash
Now, let's try to crack it using "rockyou.txt" as the wordlist and "KeePass" as the format.
ubuntu@tryhackme:~$ john -w /usr/share/wordlists/rockyou.txt --format=KeePass database.hash
Warning: invalid UTF-8 seen reading /usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (KeePass [AES/Argon2 256/256 AVX2])
Cost 1 (t (rounds)) is 20 for all loaded hashes
Cost 2 (m) is 65536 for all loaded hashes
Cost 3 (p) is 2 for all loaded hashes
Cost 4 (KDF [0=Argon2d 2=Argon2id 3=AES]) is 0 for all loaded hashes
Will run 2 OpenMP threads
Note: Passwords longer than 41 [worst case UTF-8] to 124 [ASCII] rejected
Proceeding with wordlist:/home/ubuntu/Desktop/john/run/password.lst
Press 'q' or Ctrl-C to abort, 'h' for help, almost any other key for status
Failed to use huge pages (not pre-allocated via sysctl? that's fine)
[REDACTED-PASSWORD] (.Passwords)
1g 0:00:13:53 DONE ([]) 0.001199g/s 2.578p/s 2.578c/s 2.578C/s [REDACTED-PASSWORD]
Use the "--show" option to display all of the cracked passwords reliably
Session completed
ubuntu@tryhackme:~$
Although it took a while (~15min), we were lucky and now we have a potential matching password. Let's grab it,
ubuntu@tryhackme:~$ john database.hash --show
.Passwords:[REDACTED-PASSWORD]
1 password hash cracked, 0 left
ubuntu@tryhackme:~$
and then use it to access the KeePass Password Database (".Passwords").
keepassxc .Passwords.kdbx
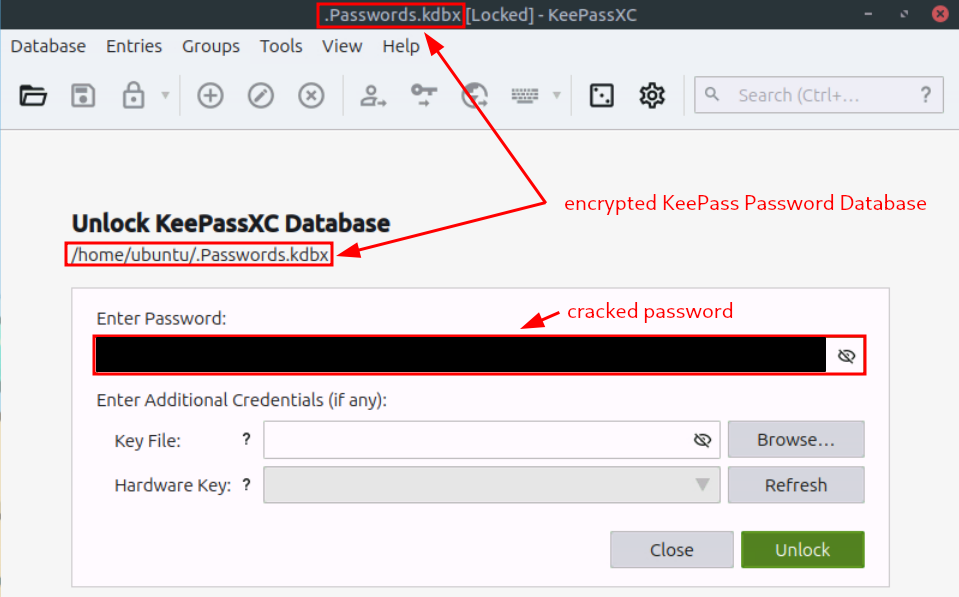
Figure 5: Using the cracked password to open the KeePass Password Database
Interestingly enough, once the password database is decrypted, only one Key named "Key" is present inside the database named "Root". Moreover, it appears to be empty, without any credentials like username or password. But once one checks the "Advanced" Tab, there is an attached image file named "sq2.png".
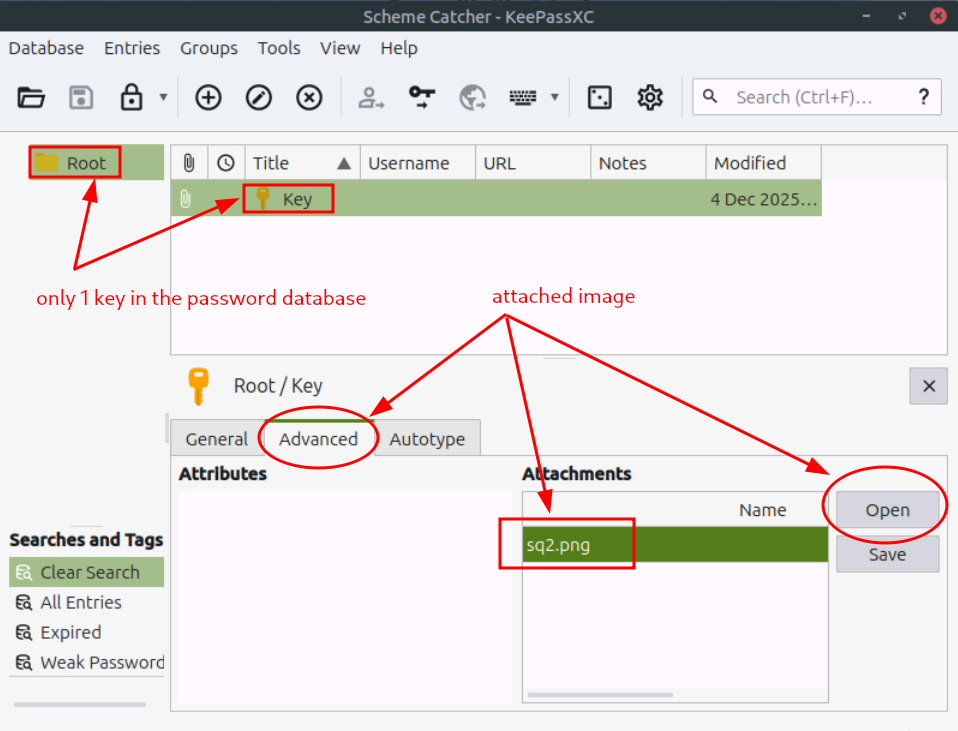
Figure 6: Attached Image inside KeePass
Opening up the attached image ("sq2.png") brings us the hidden key necessary for the Side Quest 2 Challenge.

Figure 7: Redacted Key for SideQuest 2
Bonus-Question-2: If you enjoyed this task, feel free to check out the Password Attacks room.
No answer needed